光学图像压缩加密技术研究进展  下载: 1051次封面文章特邀综述
下载: 1051次封面文章特邀综述
Advances in Optical Image Compression and Encryption Methods
1 北京工业大学理学部,北京 100124
2 南阳师范学院机电工程学院,河南 南阳 473061
图 & 表
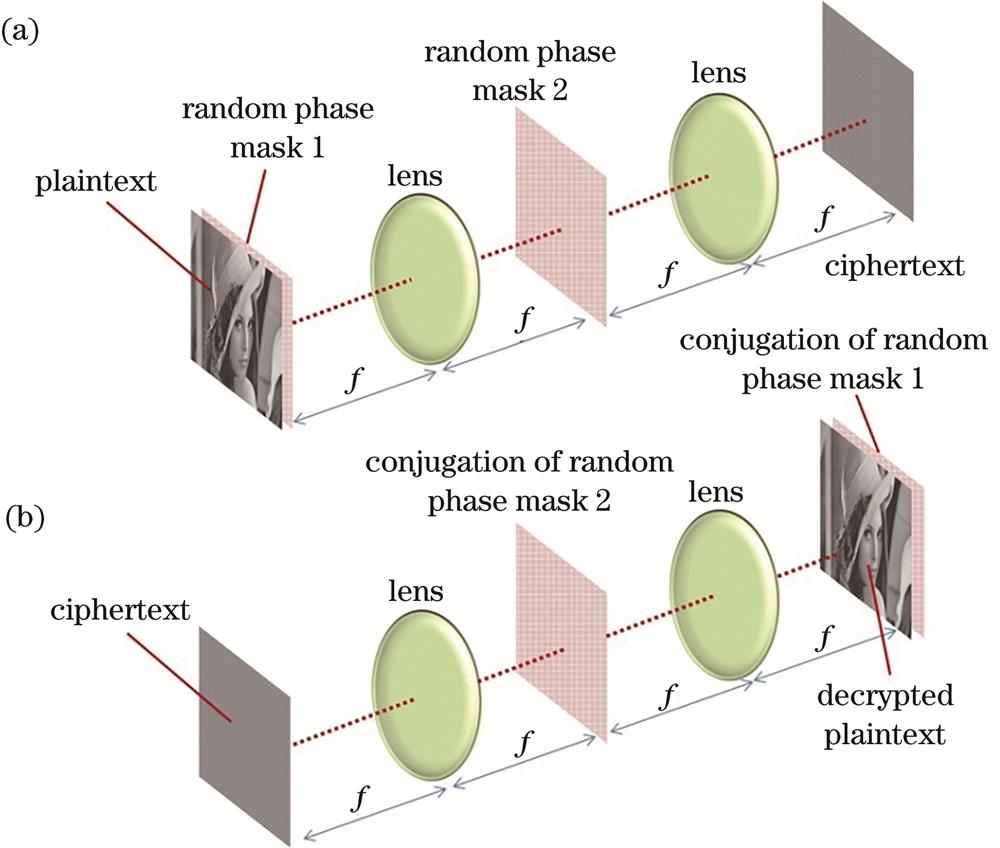
图 1. 双随机相位编码光学加密和解密方法示意图。(a)加密过程;(b)解密过程
Fig. 1. Optical implementation of double random phase encoding. (a) Encryption; (b) decryption
下载图片 查看原文
图 2. 采用不同压缩策略的光学图像压缩加密系统的信息流程示意图。(a)明文压缩;(b)密文压缩;(c)同步压缩
Fig. 2. Information processing flowchart for different compression strategies in optical compression-encryption system. (a) Plaintext compression; (b) ciphertext compression; (c) synchronized compression
下载图片 查看原文
图 3. 利用变换域能量集中性进行信息压缩的例子
Fig. 3. An example of information compression by using the concentration of energy in the transform domain
下载图片 查看原文
图 4. G-S算法的原理
Fig. 4. Principle of G-S algorithm
下载图片 查看原文
图 5. 基于压缩感知的单像素相机[41]
Fig. 5. Single pixel camera based on compressive sensing[41]
下载图片 查看原文
图 6. 基于频谱融合的双图像加密方法[44]
Fig. 6. Double-image encryption based on frequency spectral fusion[44]
下载图片 查看原文
图 7. 基于频谱融合的多图像加密方法的数值模拟结果[44]。(a)原始图像;(b)密文;(c)解密图像
Fig. 7. Simulation results of multiple-image encryption based on frequency spectral fusion[44]. (a) Original images; (b) ciphertext; (c) decrypted images
下载图片 查看原文
图 8. 基于Radon变换的多图像压缩加密方法[52]
Fig. 8. Multiple-image compression and encryption based on Radon transform[52]
下载图片 查看原文
图 9. 基于压缩感知和双随机相位编码系统的图像加密与解密流程[55]
Fig. 9. Image encryption and decryption process based on compression sensing and dual random phase coding system[55]
下载图片 查看原文
图 10. 基于压缩感知和双随机相位编码的图像加密系统的仿真结果[55]。(a)原始图像;(b)经传感矩阵降采样后的图像;(c)宿主图像;(d)密文;(e)含密文信息的宿主图像;(f)重建图像
Fig. 10. Simulation results of image encryption system based on compression sensing and double random phase coding[55]. (a) Original image; (b) image downsampled by sensing matrix; (c) host image; (d) ciphertext; (e) combined image containing cipher information; (f) reconstructed image
下载图片 查看原文
图 11. 基于空间复用和压缩感知的光学加密过程示意图[58]
Fig. 11. Schematic of optical encryption process based on spatial multiplexing and compression sensing[58]
下载图片 查看原文
图 12. 基于空间复用和压缩感知的光学解密过程示意图[58]
Fig. 12. Schematic of optical decryption process based on spatial multiplexing and compression sensing[58]
下载图片 查看原文
图 13. 基于距离复用的多图像加密技术[63]。(a)加密过程;(b)解密过程
Fig. 13. Multiple-image encryption based on position multiplexing[63]. (a) Encryption; (b) decryption
下载图片 查看原文
图 14. 基于距离复用的多图像加密系统的数值仿真结果[63]。(a)密文;(b)对应于位置的解密结果;(c)对图14(b)所示的图像进行高斯滤波的结果;(d)对应于位置处的解密结果
Fig. 14. Numerical simulation results of multiple-image encryption scheme based on position multiplexing [63]. (a) Ciphertext; (b) decryption corresponding to position ; (c) result of Gaussian filtering on the image shown in Fig. 14 (b); (d) decryption corresponding to position
下载图片 查看原文
图 15. 基于theta调制原理的多图像加密方案[71]
Fig. 15. Theta-modulation-based multiple-image encryption[71]
下载图片 查看原文
图 16. 基于theta调制原理的多图像加密的密文重建方法[71]
Fig. 16. Reconstruction of ciphertexts in theta-modulation-based multiple-image encryption[71]
下载图片 查看原文
图 17. 基于theta调制原理的多图像加密的明文重建结果[71]
Fig. 17. Reconstruction of plaintexts in theta-modulation-based multiple-image encryption[71]
下载图片 查看原文
图 18. 基于CCD旋转角度复用的多图像加密系统[75]
Fig. 18. Multiple-image encryption based on angular multiplexing of CCD[75]
下载图片 查看原文
图 19. 基于CCD旋转角度复用的多图像加密系统复合密文的频谱[75]。(a)模拟结果;(b)实验结果
Fig. 19. Spectrum of the synthetic ciphertextofmultiple-image encryption based on angular multiplexing of CCD[75]. (a) Simulation result; (b) experimental result
下载图片 查看原文
图 20. 对密文中每个像素值进行不同阶数的量化而得到的解密结果[30]。(a)4阶;(b)3阶;(c)2阶
Fig. 20. Decrypted results obtained by quantizing each pixel value in the ciphertext by different orders[30]. (a) 4 bits; (b) 3 bits; (c) 2 bits
下载图片 查看原文
图 21. 基于深度学习的光学密文压缩方法[82]。(a)压缩过程;(b)解压缩过程
Fig. 21. Optical ciphertext compression method based on deep learning[82]. (a) Compression; (b) decompression
下载图片 查看原文
图 22. 基于深度学习的光学密文压缩方法与JPEG、JPEG2000的对比[82]
Fig. 22. Comparison of the deep-learning-based optical ciphertext compression approach with JPEG and JPEG2000[82]
下载图片 查看原文
图 23. 压缩感知计算鬼成像加密系统[29]
Fig. 23. Optical encryption based on compressive ghost imaging encryption[29]
下载图片 查看原文
图 24. 压缩鬼成像加密的解密结果[29]。(a)明文;(b)采样3500次时常规方法的解密结果;(c)采样3500次时压缩感知的解密结果;(d)采样200次时压缩感知的解密结果
Fig. 24. Decrypted results using compressive ghost imaging[29]. (a) Plaintext; (b) decrypted result obtained by conventional method under 3500 samplings; (c) decrypted result obtained by compressive sensing under 3500 samplings; (d) decrypted result obtained by compressive sensing under 200 samplings
下载图片 查看原文
图 25. 基于单像素成像、相移全息以及随机相位编码的加密系统[90]
Fig. 25. Encryption system based on single pixel imaging, phase shifting holography, and random phase coding[90]
下载图片 查看原文
图 26. 加密系统对灰度图像的解密结果[90]。(a)明文;(b)DMD平面的全息图之一;(c)约256×256×42.1%次测量的重建结果,其中256×256为像素数,42.1%为采样比例
Fig. 26. Decryption result of gray image obtained by encryption system[90]. (a) Plaintext; (b) one of the encrypted holograms on the DMD plane; (c) retrieved image of about 256×256×42.1% measurements, where 256×256 denotes the pixel count and 42.1% denotes the sampling ratio
下载图片 查看原文
图 27. 基于多平面相位恢复和干涉原理的多图像加密系统的光学解密方案[93]
Fig. 27. Optical decryption scheme of multi-image encryption system based on multi-plane phase recovery and interference principle[93]
下载图片 查看原文
图 28. 基于多平面相位恢复算法和干涉原理的多图像加密系统的迭代算法[93]
Fig. 28. Iterative algorithm of multi-image encryption system based on multi-plane phase recovery algorithm and interference principle[93]
下载图片 查看原文
图 29. 基于三维空间和相位恢复算法的多图像加密方法[94]
Fig. 29. Multiple-image encryption based on 3D space and phase retrieval algorithm[94]
下载图片 查看原文
图 30. 基于角度复用和相位恢复算法的多图像加密方法[95]
Fig. 30. Multiple-image encryption based on azimuth multiplexing and phase retrieval algorithm[95]
下载图片 查看原文
图 31. 基于输入面振幅约束的迭代加密系统[97]。(a)解密光路和迭代算法依据;(b)输入平面的振幅约束;(c)输出平面振幅约束(即期望解密得到的明文)
Fig. 31. Iterative cryptosystem based on amplitude constraint in input plane[97]. (a) Decryption optical path and iterative algorithm basis; (b) amplitude constraint in input plane; (c) amplitude constraint in output plane
下载图片 查看原文
图 32. 基于空间复用的密文合成方法[97]
Fig. 32. Ciphertext combination method based on spatial multiplexing[97]
下载图片 查看原文
图 33. 基于光学系统的图像加密[98]
Fig. 33. Optical encryption based on correlator[98]
下载图片 查看原文
图 34. 基于超颖表面和迭代算法的秘密共享(多图像加密)系统[33]
Fig. 34. Secret sharing (multiple-image encryption) system based on metasurface and iterative algorithm[33]
下载图片 查看原文
图 35. 光学衍射成像加密系统
Fig. 35. Optical diffractive-imaging-based encryption scheme
下载图片 查看原文
图 36. 单次曝光光学衍射成像加密系统的解密算法效果[107]。(a)解密图像;(b)相关系数与迭代次数的关系;(c)第一阶段相关系数随迭代次数的变化;(d)第二阶段相关系数随迭代次数的变化
Fig. 36. Effect of decryption algorithm of single exposure optical diffraction imaging encryption system[107]. (a) Decrypted image; (b) dependence of CC on iteration number; (c) dependence of CC on iteration number corresponding to the first iterative procedure; (d) dependence of CC on iteration number corresponding to the second iterative procedure
下载图片 查看原文
图 37. 基于多模态相位恢复算法和焦距复用的多图像加密系统[110]
Fig. 37. Multi-image encryption system based on multimode phase retrieval algorithm and focal length multiplexing[110]
下载图片 查看原文
图 38. 基于多模态相位恢复算法和焦距复用的多图像加密系统中解密图像质量(CC)随迭代次数的变化[110]
Fig. 38. Relationship between the quality of the decrypted images (CC) and the iteration number in the multi-image encryption system based on multimode phase retrieval algorithm and focal length multiplexing[110]
下载图片 查看原文
图 39. 基于多模态衍射成像的单次曝光彩色图像加密系统[111]
Fig. 39. Single exposure color image encryption system based on multimodal diffraction imaging[111]
下载图片 查看原文
图 40. 基于压缩全息的多图像加密系统[114]
Fig. 40. Multiple-image encryption based on compressive holography[114]
下载图片 查看原文
图 41. 基于压缩全息的多图像加密系统的解密结果[114]。(a)~(c)明文;(d)全息图之一;(e)~(g)解密结果
Fig. 41. Decrypted results of multiple-image encryption based on compressive holography[114]. (a)-(c) Plaintexts; (d) one of the holograms; (e)-(g) decrypted results
下载图片 查看原文
表 1光学图像压缩加密技术的压缩策略和具体压缩方法
Table1. Compression strategies and methods for optical image compression-encryption
| Compression strategy | Compression method |
|---|
| Plaintext compression | Transform domain compression | | Compressive sensing | | Ciphertext compression | Parameter multiplexing compression | | Classical compression | | Compressive sensing | | Synchronized compression | Iterative phase retrieval algorithm | | Compressive sensing |
|
查看原文
表 2经典压缩算法直接压缩密文的压缩效果[30]
Table2. Results by applying several classical compression methods to the original ciphertext[30]
| Hol.no. | Size(kB) | LZ77(kB) | LZW(kB) | Huff.(kB) | BW(kB) | Compression ratio |
|---|
| LZ77 | LZW | Huff. | BW |
|---|
| 1 | 65,536 | 62,651 | 65,536 | 62,529 | 63,869 | 1.05 | 1.00 | 1.05 | 1.03 | | 2 | 65,536 | 62,644 | 65,536 | 62,519 | 63,836 | 1.05 | 1.00 | 1.05 | 1.03 | | 3 | 65,536 | 62,645 | 65,536 | 62,515 | 63,823 | 1.05 | 1.00 | 1.05 | 1.03 | | 4 | 65,536 | 62,643 | 65,536 | 62,515 | 63,825 | 1.05 | 1.00 | 1.05 | 1.03 | | 5 | 65,536 | 62,641 | 65,536 | 62,513 | 63,825 | 1.05 | 1.00 | 1.05 | 1.03 | | Averages: | | | | | | 1.05 | 1.00 | 1.05 | 1.03 |
|
查看原文
表 3经典压缩算法用于量化密文的压缩效果[30]
Table3. Results by applying several classical compression methods to the quantized ciphertext[30]
| Bits | Size(kB) | LZ77(kB) | LZW(kB) | Huff.(kB) | BW(kB) | Compression ratio |
|---|
| LZ77 | LZW | Huff. | BW |
|---|
| 2 | 65,536(16,384) | 47 | 42 | 1027 | 32 | 1394(349) | 1560(390) | 64(16) | 2048(512) | | 3 | 65,536(16,384) | 1138 | 1006 | 1317 | 1097 | 58(14) | 65(16) | 50(12) | 60(15) | | 4 | 65,536(16,384) | 2120 | 1963 | 1991 | 2084 | 31(7.7) | 33(8.3) | 33(8.2) | 31(7.9) | | 5 | 65,536(16,384) | 3097 | 2969 | 3021 | 2985 | 21(5.3) | 22(5.5) | 22(5.4) | 22(5.5) | | 6 | 65,536(16,384) | 4003 | 4018 | 3923 | 3901 | 16(4.1) | 16(4.1) | 17(4.2) | 17(4.2) | | 7 | 65,536(16,384) | 4732 | 5124 | 4784 | 4795 | 14(3.5) | 13(3.2) | 14(3.4) | 14(3.4) | | 8 | 65,536(16,384) | 5460 | 6236 | 5613 | 5659 | 12(3.0) | 11(2.6) | 12(2.9) | 12(2.9) |
|
查看原文
表 4各种具体压缩方法的对比与分析
Table4. Comparison and analysis of the aforementioned compression methods
| Compression strategy | Compression method | Frame | Advantages and disadvantages |
|---|
| Plaintext compression | Transform domain compression | | This method always offers high quality decryption,but the independence between the compression/decompression and the encryption/decryption leads to time consumption. | | Compressive sensing | This method always offers high quality decryption,but the decompression is time-consuming;meanwhile,the independence between the compression/decompression and the encryption/decryption leads to time consumption. | | Ciphertext compression | Parameter multiplexing compression | | This method always suffers from low-quality decrypted results caused by cross-talk noise,but the decompression and decryption are always carried out simultaneously with a pure optical manner. Some preprocessing or postprocessing approaches can be adopted to alleviate the cross-talk noise at the cost of time. | | Classical compression | The independence between the compression/decompression and the encryption/decryption leads to time consumption. The quality of the decryption will seriously degrade in the case of a high compression ratio;however,deep learning provides a new avenue for coping with such issues. | | Compressive sensing | This method enables simultaneously compression and encryption,and it is widely used in cryptosystems based on ghost/single-pixel imaging. This method can always achieve a high compression ratio,but the decryption(decompression)is time-consuming. | | Synchronized compression | Iterative phase retrieval algorithm | Iteratively encryption,optically decryption | The encryption procedure is time-consuming,but the decryption(decompression)can always be performed optically. The quality of the decrypted images is relatively high. | | Optically encryption,iteratively decryption | The encryption procedure can always be performed optically,but the decryption(decompression)procedure is time-consuming. The quality of the decrypted images is relatively high. | | Compressive sensing | | This method enables simultaneously compression and encryption with a pure optical manner,but the decryption(decompression)procedure is time-consuming. |
|
查看原文
秦怡, 满天龙, 万玉红, 王兴. 光学图像压缩加密技术研究进展[J]. 激光与光电子学进展, 2023, 60(4): 0400001. Yi Qin, Tianlong Man, Yuhong Wan, Xing Wang. Advances in Optical Image Compression and Encryption Methods[J]. Laser & Optoelectronics Progress, 2023, 60(4): 0400001.
 下载: 1051次封面文章特邀综述
下载: 1051次封面文章特邀综述